In the past, I wrote an article about a very easy way to mount and explore a TrueCrypt volume in one step. Some security issues came up about keeping the volume password in the batch file used to mount. This new article take that into account. The [almost] same script is used to mount the volume, but the password is taken out and you are instead required to enter the password at a prompt. The beginning steps are the same as the previous article, so if you just want to see the new feature, skip down to the “Create a script to mount” section.
Create your volume
Create any size TrueCrypt volume using your encryption algorithm of choice. My computer runs the Blowfish algorithm the fastest, so that’s my typical choice. Make sure you assign a good, long, hard-to-break password to it. The only way to reveal the contents of the volume is the password. We’re talking encryption standards the government uses here. So no one’s going to break in another way — you need a good password and you must remember it.
Copy TrueCrypt stand-alone files
TrueCrypt comes in an installable version and an stand-alone version. You can use the stand-alone command-only version for the batch script. The stand-alone files are inside the “Setup Files” folder inside the TrueCrypt folder. First, rename truecrypt.sys to tc.sys and truecrypt-x64.sys to tc-x64.sys. This will make it more simple for us. Go ahead and copy tc.sys and tc-x64.sys to C:\WINDOWS\. This will allow us to call the TrueCrypt program in the batch script.
Create a script to mount (NEW stuff here)
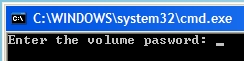
You may download the new batch script I wrote to mount a volume. Make sure you fill in the appropriate part specific to you — the path to your volume. Place this script in C:\WINDOWS\ so you can call it from the Run box. Here’s the main line in the script which has been slightly changed from the previous version:
tc /v <path to file> /l x /p %thepass% /q
As I said, make sure you fill in the correct path to your file. The changed piece is the pulling of the password and the addition of the %thepass%. That will require you to enter a password through a prompt when you run the script. Your password will no longer be in the file for anyone to see.
You may notice, I use various flags in the call. The /v flag will make TC mount a volume; then /l x will mount it as the letter X:\ (like it’s a drive); /p means the password follows it — where in this case, it causes a prompt. Finally, /q will quit the program when done. After the mounting takes place, we call explorer on the X:\ drive to open it.
Create a script to unmount
Following the previous script’s example, I’ve also written a script to unmount your volume. Fill in the necessary changes. Place this script in C:\WINDOWS\ so you can call it from the Run box. The only new flag I use is /dx which will dismount the X:\ drive.
Test it out
Time to test it all out. Hit WinKey + R > type in mount2 (or you can rename my new script to mount.bat or whatever you want) and hit Enter. Your volume should mount and should open in Windows Explorer. Now, to unmount it, in the Run box, type in unmount (or whatever you may want to rename it to) and hit Enter. Nextel. Done.
Too bad you can’t mask the password in the command prompt.
Tim,
I feel the same way. The way I think about it…if you are mounting a secure volume, no one should be around you that you don’t trust.
If anyone does know of a way to mask the password input, please let me know in the comments or by email.
This is a great idea. I previously had truecrypt installed, but am getting the following error when trying to run the script:
‘The path X:\ does not exist or is not a directory’.
I tried to run ‘tc’ from the command prompt and that doesn’t work either (renamed files are in the c:\windows folder). Any suggestions?
Mark,
I’ve adapted your script with a method that does not display the password. Full details and the new script are here: http://securitymusings.com/article/88/easy-truecrypt-volume-mounting
Note that this will work with Windows XP, Windows Server 2003, and later only. The component that masks the passwords is not present in Windows 2000.
My install named TC in full : truecypt.
I use the following script:
“C:\Program Files\TrueCrypt\TrueCrypt” /a favorites /p **PASSWORD** /q
Note the quotes. I have the needed volumes set as favorites.
As for the batch file, well I have that stored on a datakey.
or of course you could use bat2exe to hide the code:
http://www.computerhope.com/dutil.htm
@ Basho
You don’t need to hide the code, as it doen’t contain the password in any way or form. It only uses the variable ‘thepass’ which contains any string of letters you entered. So there is no way for anyone to read your password from the file, only when you physically enter the password can anyone read it over your shoulder or via a keylogger.
You can mask passwords in a batch file. Check out this bat file.
http://www.ericphelps.com/batch/samples/hta_password.bat.txt
It makes an HTA file for the password input.
Ben,
The error you are getting means X:\ hasn’t been mounted so Explorer can open it. That means something went wrong in the mounting part. If you moved the files to C:\WINDOWS\ and you can’t run tc from cmd then you may have the wrong name for tc. You don’t actually have to rename truecrypt.sys to tc.sys, but I did for the sake of simplicity in the script. If you choose not to, edit the script from tc … to truecrypt ….
Also, you can try what Basho did by calling the full path to TrueCrypt. Make sure you wrap quotes around the path since spaces are involved.
Peter,
Thanks, I’ll add a link to your adaption soon.
Basho,
I like your idea of just calling the TC from the real path in Program Files. I also thought about using the bat2exe, but I figured people could do that themselves if they have the need to cover the script’s code.
oCfuu,
That’s exactly how I feel. You shouldn’t really care if the password isn’t masked because you shouldn’t be mounting in front of anyone else that you don’t trust. Obviously some people have found ways to mask the password which is great for that extra security if you need it. I guess my original script has lots of potential for extra amounts of additional security.
Lipsore,
Thanks for the link – it looks interesting. I’ve only created one Hypertext Application, so I’m not too familiar with HTAs in general, but that looks like a possible way to mask the password.
Why not just remove the password flag entirely? I’ve bound the following to a key press:
truecrypt.exe /v /d /q
When I run that, I get a nice popup prompt for the password that masks the password as I type it.
grrrr, the command line params were eaten by the html. That should be:
truecrypt.exe /v file /d drive /q
The ultimate script would give the option of using a password that consisted of mouse clicks so keystroke recorders couldn’t be used.
Another nice feature for mount2.bat would be that the script would dump back to windows instead of stating “incorrect truecrypt password”. In this way you could replace the line “enter password” for something like “format c? y/n” so that if the file was opened by accident, the bad guys wouldn’t know what they just ran across.
Jim,
When I was first writing the script and testing it, that’s what happened to me. Instead of %thepass%, I used %1 for Run box input. It didn’t really work because it caused the TrueCrypt password box to pop up. If you like that idea, by all means, use that method by taking out the password section completely. Most of the work is done for you, now its up to you to customize parts to your liking.
nitecrlwr,
You have some good ideas there. I like the idea of tricking malicious users to scare them.
I’ve had so many good comments about this method. I plan to sift through various features and I’ll get around to creating a third version. It will take some time since I’m quite busy with school, but stay tuned to the blog.
In case you wonder what else you can do with TrueCrypt via its command line interface, see the official docs:
http://www.truecrypt.org/docs/?s=command-line-usage
This thing rocks – I’ve also formatted a partition but can’t seem to get it to mount the partition. Any ideas? Thanks, MH
Note, you are also giving around the location of your “hidden” encrypted file in the script. So you are trading Plausible Deniability for easy of use.
MH,
You formatted a full partition? Can you give more details about it?
Technocrat,
Good point, however, if that’s a problem, it’s easy to just add a new variable to the script to abstract the path. You can make a new script that requires you to enter the path and the password. By logic, even having the script at all says that you are using TrueCrypt. The purpose of the script it to make it quicker to mount the volume. Thanks for pointing that out though.
I’m confident I’ve followed all the steps, but I get a command line error saying that the application cannot be run in win32 mode.
I’ve tried using tc, and also using the full path in quotes as Basho suggested.
I’m using Windows XP Professional.
The entire password thing is no longer an issue, as the latest version of TrueCrypt displays a dialog when used with /q. The password that you type is hidden. So mounting is easy with
TrueCrypt.exe /v /l /q
That was:
TrueCrypt.exe /v [file] /l [drive] /q
Thought html like stuff would be escaped instead of cut out
Blizz,
TC always had that prompt if you didn’t supply a password though the command line. The purpose of the command-based launch (well…my original intention) makes it seem like you don’t even have TC — with the prompt, it quite obvious that TC is being used.
If there is a password on the file and you remove the
/p passwdthen TC will prompt for a password in its own prompt.Just add a shortcut of TrueCrypt.exe to Windows Startup menu. On every boot, it will run and prompt you to specify the volume location (can save in history for ease) and password and will mount the file/partition. No scripts needed!!
To mount a partition instead of a file, use the following syntax.
c:\progra~1\Truecr~1\truecr~1.exe /v \Device\Harddisk0\Partition5 /l F /p %thepass% /q
This batch file is calling the truecrypt exe in it’s installed location, mounting my partition #5 (on my first harddrive) as drive F. Truecrypt will supply the prompting for the password.
Provided you place the batch file in your path, you can run this batch file from the RUN prompt, Command Prompt, or create a Shortcut on the desktop.
RE: Automount TrueCrypt volumes;
Do you know of a way to map a mounted truecrypt volume to a folder as is possible on regular partitions and PGPWDE encrypted volumes. PGPWDE encrypted volumes retain their original drive letter, unlike truecrypt volumes which cannot do so. If TrueCrypt could map volumes to empty folders, then the need for the drive letters to remain open is eliminated. This would solve some drive letter conflicts found in TrueCrypt.
great tutorial!
@nitecrlwr: I’ve attached a sample script for ‘silent’ launch.
‘MapName’ (optionally) maps a drive letter with a custom label.
–any.bat–
@echo off
cls
echo Reinstall bluetooth device driver? Y/N
set /P thepass=””
c:\progra~2\TrueCrypt\TrueCrypt.exe /v C:\FILE /cn /hn /lx /mrm /e /a /p %thepass% /silent /q
MapName.bat X: “LABEL” Status
cls
exit
–MapName.bat —
@echo off
if {%3}=={} @echo Syntax MapName Drive NewName OK&goto :EOF
setlocal
set drv=%1
set drv=%drv:”=%
set nn=%2
set nn=%nn:”=%
set mn=”%TEMP%\MapName_%RANDOM%.VBS”
set er=”%TEMP%\MapName_%RANDOM%.TMP”
if exist %er% del /q %er%
@echo Set oShell = CreateObject(“Shell.Application”)>%mn%
@echo DRIVE = “%drv:~0,1%:\”>>%mn%
@echo oShell.NameSpace(DRIVE).Self.Name = “%nn%”>>%mn%
set OK=N
call :quiet>%er% 2>&1
del /q %mn%
call :sz %er%
del /q %er%
endlocal&set %3=%OK%
goto :EOF
:sz
set /a size=%~z1
if %size% EQU 0 set OK=Y
goto :EOF
:quiet
cscript //nologo %mn%
.. just forgot to mention:
You could also compile both batch files to an executable, e.g. I use Quick Batch file compiler (which is not free).
Change this line to include the mapping feature:
%MYFILES%\MapName.bat X: “LABEL” Status
I get an error that says ‘tc’ is not recognized as an internal or external command.
You mentioned copying over tc.sys after renaming it. Did you mean renaming truecypt.exe to tc.exe?
@freddy: the files you need to copy are from the stand-alone version of TrueCrypt, not the installable version.
How Do you automate this so you can mount an image on a flashdrive. with the program installed to the flash drive
For the security/privacy conscious people out there, you should be carefull how you use these scripts. When an environment variable is set, it is also available for reading.
Try this:
open command prompt and run your script mount2.bat entering password as it requests.
type set|sort|more and have a look for the variable called thepass. Are you happy your password is clearly visible?
C
Hi,
Is there any way that we can create encryted file container using command line in windows?
I found documentation on mounting/dismounting the existing files/volumes from command line.